State of the art developer monitoring and leak discovery service. Identify software security problems across the entire developer estate.
State of the art developer monitoring
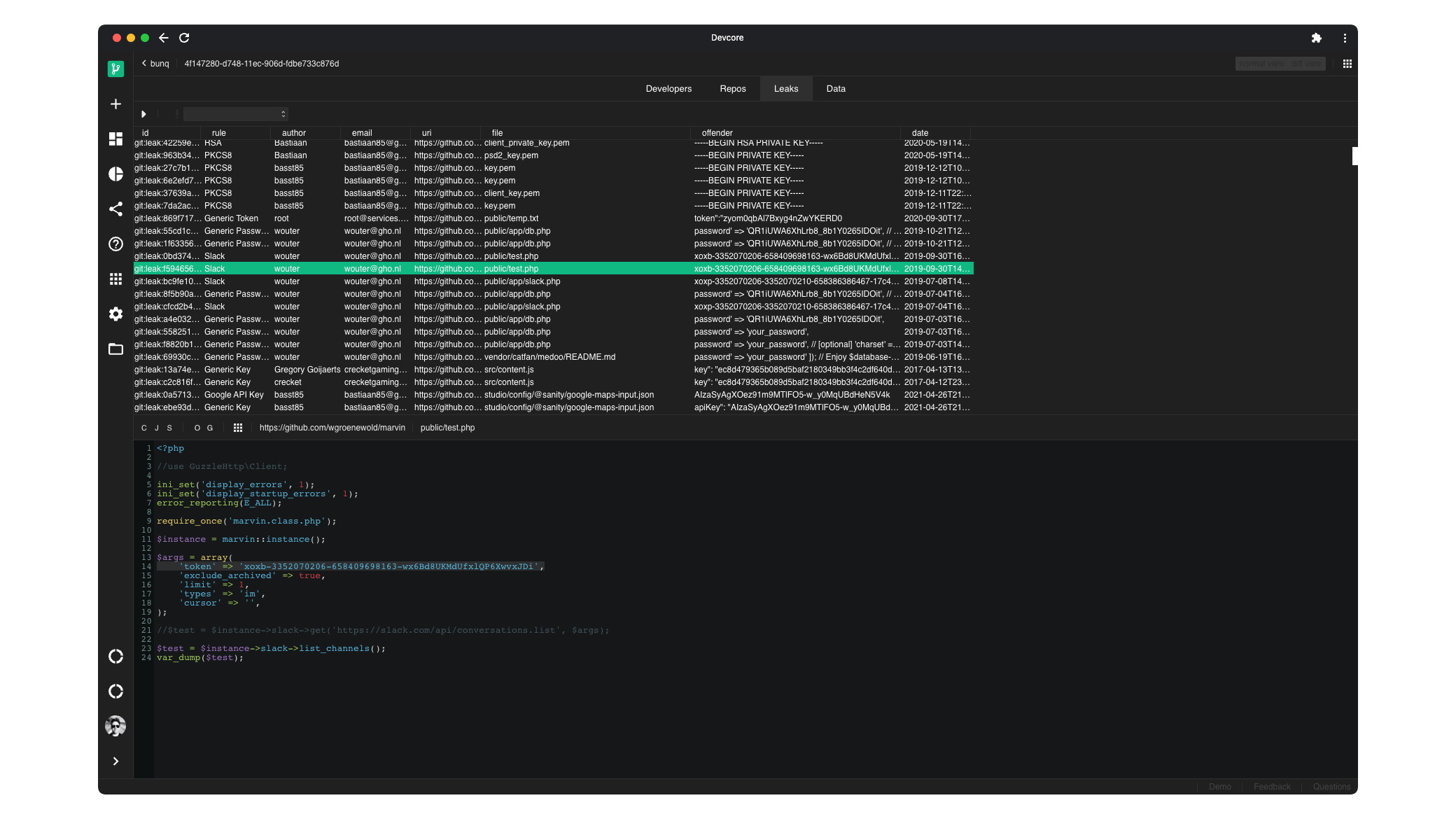
Devcore is state of the art developer monitoring and leak discovery service that helps organisations identify software security problems across the entire developer estate - from GitHub repositories owned by individual-contributors to organisation accounts, language-specific software packages and more.
Discover Everything
Devcore automatically finds all developers associated with your public organisation profile and scans for additional developer resources such as docker images, software packages published in NPM, Ruby Gems and more.
Indetify leaks in minutes
Get answers to complex questions which require access to expensive data analysis backed by super-large data pipelines.
The most throughout security development tool that goes beyond standard git repositories.
Cost-effective solution that scales to hundreds of terabytes of source data.
Identify 3rd-party developers associated with your organisation and assess your supply-chain risks.
Prevent 2nd-degree secrets leaks that could lead to developer compromise.
Automatically scrub passwords from known leaked password databases.
Provides advanced filter and code-analysis features.
Source code health check and monitoring
1000+
Developer targets
1GB+
Execution snapshots
24H+
Runtime hours
Explore use cases
Supply Chain Attacks Mitigation
Learn how Devcore can help mitigate supply chain attacks
Learn more
Secret Leakage Detection
Discover leaked secrets in yours and your contributors' code repositories.
Learn more
Frequently Asked Questions
Devcore is a state of the art developer monitoring and leaks discovery tool which helps you identify software security problems across the entire developer estate.