A holistic view across multiple targets. Domain-wide web application security scanning at its best.
A holistic view across multiple targets
SecApps Lookout is an automated web application security testing solution suitable for targeted and wide-area web security scanning. Provide the application URLs or domain names to scan and let Lookout do the rest.
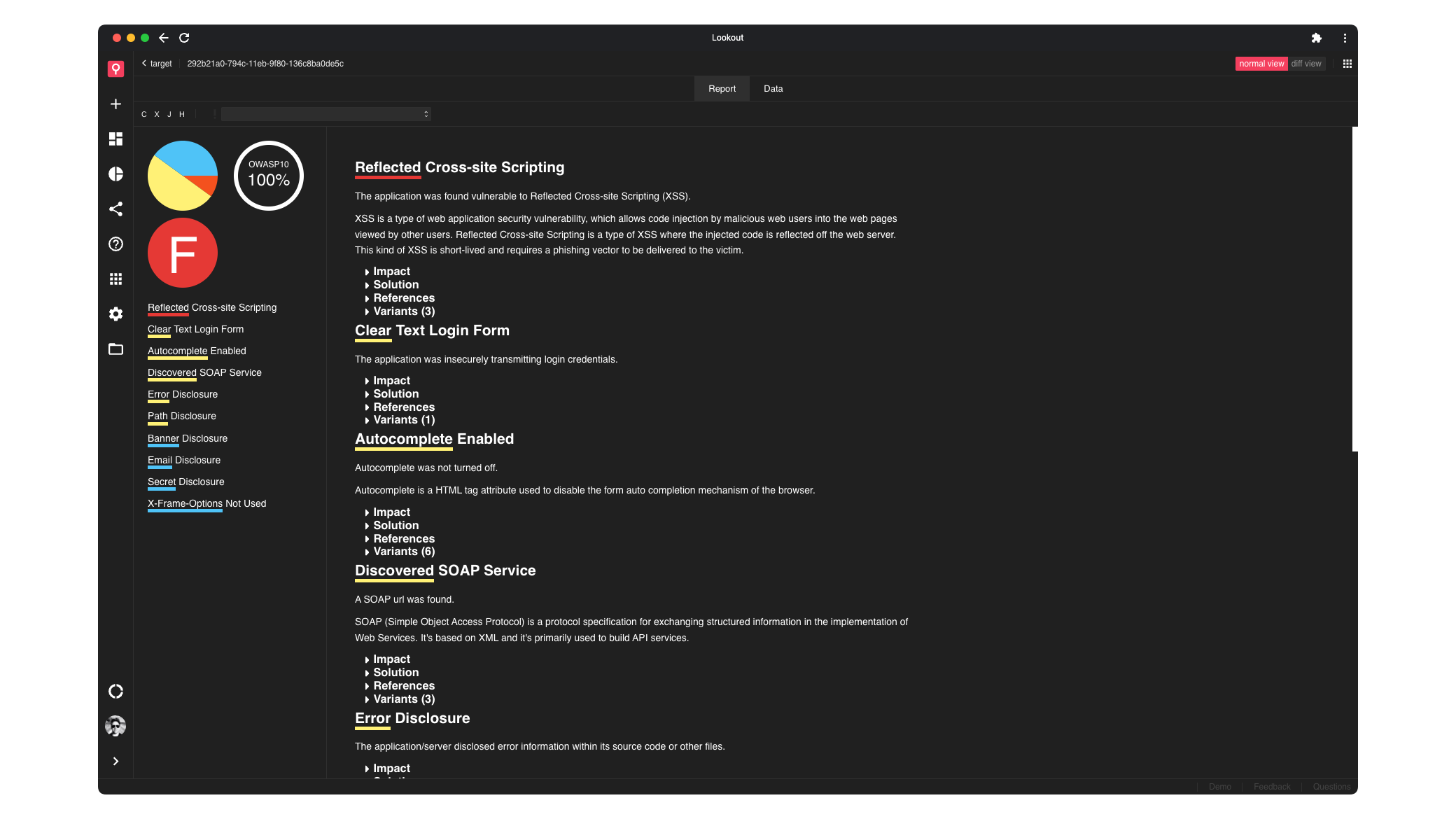
60+ vulnerability classes
The Lookout scanner can detect a wide range of security vulnerabilities from SQL Injection, Command Injection and Cross-site Scripting, host header injection, server and application misconfigurations and much more.
Web application security solution for every job
Lookout is backed by a custom web security scanning technology that packs years of Research & Development investments. Benefit from scanning technology that is not available in any other shape and form.
Vulnerability classes such as SQL Injection, Cross-site Scripting and others
Suitable for bug bounty hunting, continuous monitoring, pentesting and more
Notify team members when scans are completed for a timely analysis
Built-in mechanism to compare results with previous scans
Automatically curates a vulnerability catalogue
Data can be sent to internal and 3rd-party systems
Web application security testing at inifinite scale
100+
Testing modules
60+
Generic vulnerability classes
1GB
Execution snapshots
Explore use cases
Wide Web Application Security Scanning
SecApps Lookout is a wide web application security scanner that is designed to scan multiple web applications for vulnerabilities.
Learn more
Automated Security Testing
Setup targeted scans to fully test specific parts of your web application infrastructure.
Learn more
Frequently Asked Questions
SecApps Lookout is an automated web application security scanning solution for continuous vulnerability assessments, monitoring and bug bounty hunting.